About USB Settings¶
USB Overview¶
From the AWI and Management Console 3.1 or later, you can configure access to the host PC operating system for USB devices plugged into PCoIP Zero Client USB ports. PCoIP Management Console, configurations are found in the PCoIP Management Console Administrators' Guide.
USB device bridging
USB bridging to the host PC is supported by PCoIP Zero Clients
USB plug events are blocked in the Tera2 PCoIP Zero Client firmware by configuring the Unauthorized Devices in its AWI. The PCoIP Remote Workstation Card can also be configured to block USB device access to the host PC for an additional layer of security.
The USB permissions page is available on the PCoIP Remote Workstation Card and has a higher priority than the configurations on the PCoIP Zero Client and thus overrides the client USB permissions. It is strongly recommended you only set the USB permissions on the host when connecting to a PCoIP Remote Workstation Card from a PCoIP Zero Client. The following rules apply:
-
If the host has permissions programmed (authorized and/or unauthorized), the permissions are sent to the client. If the client has any unauthorized devices, they are added to the host’s unauthorized devices and the consolidated list is used.
-
If the host does not have permissions programmed, the client’s permissions are used.
The factory defaults have no USB permissions configured on the host. The factory defaults for the client USB permissions are 'any, any, any' (that is, authorized USB devices).
The host USB permissions are only updated at the start of a PCoIP session. They are authorized in the following order of priority (from highest to lowest):
-
Unauthorized Vendor ID/Product ID
-
Authorized Vendor ID/Product ID
-
Unauthorized Device Class/Sub Class/Protocol
-
Authorized Device Class/Sub Class/Protocol
Configuring USB Permissions from the AWI¶
From the AWI, you can configure USB permissions to authorize certain USB devices bridged to the host PC to access the host operating system or add an additional layer of security by unauthorizing USB devices trying to access the host PC operating system.
From the AWI USB permissions page, you can configure USB permissions and:
-
authorize and unauthorize a list of USB devices based on ID or Class. You can use wildcards (or specify any) to reduce the number of entries needed to define all devices.
-
configure devices that are bridged to the host that are allowed to access the host PC operating system.
USB Permissions Page¶
The following categories display on the AWI Permissions > USB page:
| Category | Description |
|---|---|
| Authorized Devices | Specify the authorized USB devices for the device: Add New: add a new device or device group to the list. This allows USB authorization by ID or Class:
|
| Unauthorized Devices | Specify the unauthorized USB devices for the device. Add New: add a new device or device group to the list. This allows USB devices to be unauthorized by ID or Class:
|
To configure USB settings:
-
From the AWI, select Configuration > USB.
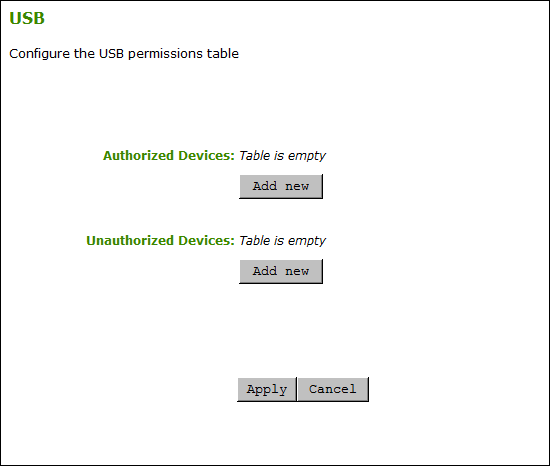
AWI USB permissions page -
From the AWI USB page, update the USB settings by selecting Add new and configure the required parameters. The parameters that display depend on whether you describe the device by Class or ID.
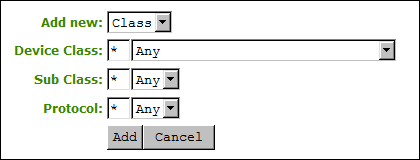
Device Class parameters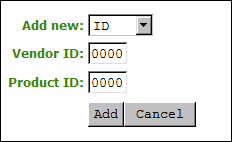
Device ID parameters -
Click Add.
-
Click Apply.
USB Configuration Parameters¶
The following parameters display when you authorize or unauthorize USB device parameters:
| Parameter | Description |
|---|---|
| Add new | When adding a new USB authorization or unauthorization entry, select one of the following:
|
| Device Class | This field is enabled when Class is selected. Select a supported device class from the drop-down menu, or select Any to authorize or unauthorize (disable) any device class. |
| Sub Class | This field is enabled when Class is selected. Select a supported device sub class from the drop-down menu, or select Any to authorize or unauthorize (disable) any sub-class. Note: If Any is selected as the device class, this will be the only selection available. |
| Protocol | This field is enabled when Class is selected. Select a supported protocol from the drop-down menu, or select Any. Note: If Any is selected as the device class or sub-class, this will be the only selection available. |
| Vendor ID | This field is enabled when ID is selected. Enter the vendor ID of the authorized (or unauthorized) device. The valid range is hexadecimal 0-FFFF. |
| Protocol ID | This field is enabled when ID is selected. Enter the product ID of the (authorized or unauthorized) device. The valid range is hexadecimal 0-FFFF. |