Configuring firewalld after an RPM Upgrade to Management Console 20.04 or newer¶
In Management Console releases 19.05 through 20.01, RPM installation disabled firewalld, enabled iptables and created rules that allowed Management Console to work as expected. Starting with release 20.04, Management Console disables iptables, enables firewalld, and leaves the firewall configuration in the hands of the local administrator.
If you are upgrading from Management Console release 19.05 through 20.01 to release 20.04 or newer using Management Console RPM, existing firewall configurations will have to be re-applied to the upgraded version of Management Console.
If you decide to use firewalld, the following instructions provide the steps to remove the iptables configuration applied by Management Console and steps to add firewalld rules required by Management Console to operate properly. Additional rules required to comply to your corporate security policy must be added by the administrator.
To remove previously installed iptables rules and add firewalld rules for use with Management Console, perform the following steps:
-
Login to Management Console console using an SSH client (e.g. putty).
-
Check iptables status(which should be active).
sudo systemctl status iptables
-
Check the applied iptables rules.
sudo iptables -L
-
Remove rule which enabled port 8080.
sudo iptables -D INPUT -p tcp -m state --state NEW --dport 8080 -j ACCEPT -
Remove rule which enabled port 8443.
sudo iptables -D INPUT -p tcp -m state --state NEW --dport 8443 -j ACCEPT -
Remove rule which enabled port 5172.
sudo iptables -D INPUT -p tcp -m state --state NEW --dport 5172 -j ACCEPT -
Remove rule which allowed incoming and outgoing pings.
sudo iptables -D INPUT -p icmp --icmp-type echo-request -j ACCEPT sudo iptables -D OUTPUT -p icmp --icmp-type echo-reply -j ACCEPT sudo iptables -D OUTPUT -p icmp --icmp-type echo-request -j ACCEPT sudo iptables -D INPUT -p icmp --icmp-type echo-reply -j ACCEPT
-
Remove PREROUTING rule.
sudo iptables -t nat -D PREROUTING -iip addr show | grep "state UP" | head -1 | awk -F': ' '{print $2}'-p tcp --dport 443 -j REDIRECT --to-port 8443 -
Drop incoming packets to 127/8 from other interfaces other than loopback interface.
sudo iptables -D INPUT -i lo -j ACCEPT sudo iptables -D INPUT -i lo -d 127.0.0.0/8 -j REJECT
-
Remove outbound traffic rule.
sudo iptables -D OUTPUT -j ACCEPT -
Remove logging rule.
sudo iptables -D INPUT -m limit --limit 5/min -j LOG --log-prefix "iptables denied: " --log-level 7 -
Remove rule which dropped packets not matching any other rule.
sudo iptables -D INPUT -j DROP sudo iptables -D FORWARD -j REJECT
-
Save iptable sevice to save your changes (should show status OK).
sudo service iptables save -
Restart iptables to apply your changes.
sudo systemctl restart iptables -
Check iptables rules (should not contain rules which Management Console install previously added).
sudo iptables -L
-
Mask iptables.
sudo systemctl mask iptables -
Stop iptables service.
sudo systemctl stop iptables -
Unmask firewalld, (should show removed symlink).
sudo systemctl unmask firewalld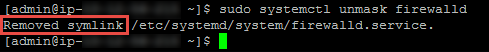
-
Enable firewalld.
sudo systemctl enable firewalld --now -
Start firewalld.
sudo systemctl start firewalld -
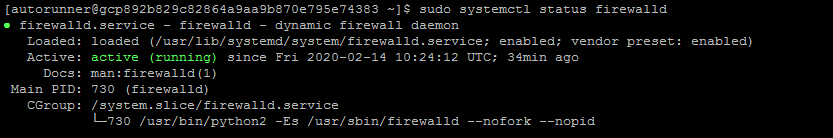
Check firewalld status (should be active).
sudo systemctl status firewalld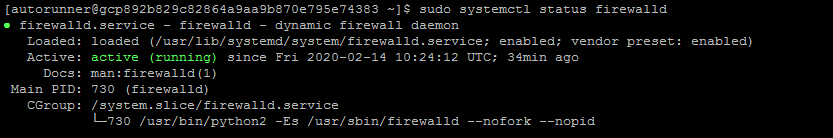
-
Get the default zone. If the default zone is trusted it will allow all packets. It is recommended that the default zone is set to public.
sudo firewall-cmd --get-defaultIf default zone is not public, execute the following commands to set the default zone to public.
sudo firewall-cmd --permanent --zone=trusted --remove-service=pcoip-agentsudo firewall-cmd --set-default=publicsudo firewall-cmd --reload
-
-
Get the default zone and assign it to a variable.
def_zone=$(firewall-cmd --get-default) -
Set the log.(all denied packets logged together)
sudo firewall-cmd --set-log-denied=all -
Add an interface.
sudo firewall-cmd --zone=$(echo $def_zone) --change-interface=$(ip addr show | grep "state UP" | head -1 | awk -F': ' '{print $2}') -
Enable required ports.
sudo firewall-cmd --zone=$(echo $def_zone) --permanent --add-port={80,443,22,5172}/tcp -
Allow pings.
sudo firewall-cmd --zone=$(echo $def_zone) --permanent --remove-icmp-block={echo-reply,echo-request} 2>/dev/null -
Redirect port 443 to 8443.
sudo firewall-cmd --zone=$(echo $def_zone) --permanent --add-forward-port=port=443:proto=tcp:toport=8443 -
Enable IP Masquerading.
sudo firewall-cmd --zone=$(echo $def_zone) --permanent --add-masquerade -
Redirect Port 80 to 8080.
sudo firewall-cmd --zone=$(echo $def_zone) --permanent --add-forward-port=port=80:proto=tcp:toport=8080 -
Drop incoming packets to 127/8 from other interfaces other than loopback interface.
sudo firewall-cmd --permanent --new-zone loopback 2>/dev/null sudo firewall-cmd --permanent --zone=loopback --change-interface=lo 2>/dev/null sudo firewall-cmd --zone=loopback --permanent --set-target=ACCEPT sudo firewall-cmd --zone=loopback --permanent --add-source=127.0.0.0/8
-
Reload the firewall rules.
sudo firewall-cmd --reload -
Confirm the rules are applied.
-
Check the firewalld status is active.
sudo systemctl status firewalld
-
Verify all rules are added in firewalld, all rules should be applied.
sudo firewall-cmd --list-all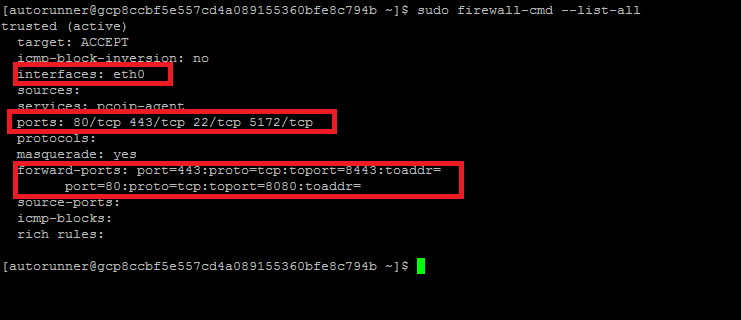
-
-
Install Management Console RPM
sudo rpm -Uv --force <RPMLink> -
Confirm RPM upgrade is working with new firewall rules by using Management Console when logged in.
Firewalld Script¶
Teradici has provided instructions to create a script that will apply firewalld rules that allow Management Console to work correctly.
Instructions on creating and executing the script can be found here