Troubleshooting Connectivity Issues¶
Network Connectivity Problems¶
Connectivity issues are often caused by firewall misconfiguration. If you are unable to establish PCoIP connections, verify that sent packets are actually being received at the intended destination.
Useful tools for troubleshooting this type of issue are ssldump or tcpdump (for Linux), or Wireshark (for Windows).
The network connections between the following endpoints all need to be operational for a PCoIP session to be successful.
| Connection | Port | Source |
|---|---|---|
| PCoIP Connection Manager | 443 TCP | PCoIP Client |
| Connection Broker | 443 (configurable) TCP | PCoIP Connection Manager |
| PCoIP Agent | 60443 TCP | PCoIP Connection Manager |
| When Security Gateway is enabled | ||
| PCoIP Security Gateway | 4172 TCP/UDP | PCoIP Client |
| PCoIP Agent | 4172 TCP/UDP | PCoIP Security Gateway |
| When Security Gateway is disabled (Direct Connection) | ||
| PCoIP Agent | 4172 UDP/TCP | PCoIP Client |
Methods for testing communication between components on required ports are given next:
- PCoIP Client to PCoIP Connection Manager
- PCoIP Connection Manager to Connection Broker
- PCoIP Connection Manager to PCoIP Agent
- PCoIP Client to PCoIP Security Gateway
- PCoIP Security Gateway from PCoIP Client (UDP)
- PCoIP Agent from PCoIP Client (UDP)
Methods are also given for verifying the component availability:
- Verifying PCoIP Agent availability
- Verifying Connection Broker availability
- Verifying PCoIP Connection Manager Web Application Availability
Connectivity from PCoIP Client to PCoIP Connection Manager¶
This check looks for traffic between the PCoIP Client and the PCoIP Connection Manager on TLS port 443.
To verify connectivity from a PCoIP Client to PCoIP Connection Manager:
-
On the server hosting the PCoIP Connection Manager, start
ssldump:sudo ssldump -i <interface> host <client-ip-address> port 443 -
From the client, connect to the PCoIP Connection Manager.
-
In the ssldump output, look for packets originating from the PCoIP Client.
Connectivity from PCoIP Connection Manager to Connection Broker¶
This check looks for traffic between the PCoIP Connection Manager and a broker on TLS port 443.
To verify connectivity from the PCoIP Connection Manager to a connection broker connectivity:
-
On the server hosting the connection broker, use ssldump or Wireshark to capture packets from the PCoIP Connection Manager on TLS port 443.
-
From the client, connect to the PCoIP Connection Manager.
-
Try to authenticate.
-
Verify from ssldump or Wireshark output that the connection broker is receiving data from the PCoIP Connection Manager.
Connectivity from PCoIP Connection Manager to PCoIP Agent¶
This check looks for traffic between the PCoIP Connection Manager and a PCoIP Agent on TLS port 60443.
To verify PCoIP Connection Manager to agent collectivity:
-
On the PCoIP agent machine, use ssldump or Wireshark to capture packets from the PCoIP Connection Manager on TLS port 60443.
-
From the client, connect to the PCoIP Connection Manager.
-
Try to authenticate and establish a session.
-
Select a resource and connect.
-
Verify from ssldump or Wireshark output that the PCoIP agent is receiving data from the PCoIP Connection Manager.
Connectivity from PCoIP Client to PCoIP Security Gateway¶
This check looks for traffic between the PCoIP client and the PCoIP Security Gateway on TLS port 4172.
To verify that the PCoIP Security Gateway server is receiving session initiation data from the PCoIP client:
-
On the server hosting the PCoIP Security Gateway, start ssldump:
sudo ssldump -i <interface> host [client-ip-address] and port 4172 -
From the client, connect to the PCoIP Connection Manager.
-
Try to authenticate and establish a session.
-
Select a resource and connect.
-
Verify from ssldump output that the PCoIP Security Gateway is receiving data from the client.
Note: Firewall must allow traffic on UDP:4172
If the firewall is configured to enable TCP traffic over port 4172 but not UDP traffic, then the ssldump output will show packets but you won't be able to establish a PCoIP session.
Connectivity (UDP) to PCoIP Security Gateway from PCoIP Client¶
This check looks for UDP traffic between the PCoIP Security Gatway and the PCoIP client on TLS port 4172.
To verify that the PCoIP Security Gateway is receiving UDP traffic from the PCoIP client:
-
On the server hosting the PCoIP Security Gateway, start tcpdump:
sudo tcpdump -i <interface> host [client-ip-address] and -n udp port 4172 -
From the client, connect to the PCoIP Connection Manager.
-
Try to authenticate and establish a session.
-
Select a resource and connect.
-
Verify from ssldump output that the PCoIP Security Gateway is receiving data from the client.
Connectivity (UDP) to PCoIP Agent from PCoIP Client¶
This check looks for UDP traffic between the PCoIP Security Gatway and the PCoIP client on TLS port 4172.
To verify that the PCoIP server is receiving UDP traffic from the PCoIP client:
-
On the server hosting the PCoIP server, start tcpdump:
sudo tcpdump -i <interface> host [server-ip-address] and -n udp port 4172 -
From the client, connect to the PCoIP Connection Manager.
-
Try to authenticate and establish a session.
-
Select a resource and connect.
-
Verify from ssldump output that the PCoIP server is receiving data from the client.
Verifying PCoIP Agent Availability¶
Ensure your DNS is configured correctly, then verify you can establish and maintain a connection to the agent.
For each virtual desktop host in your deployment or RDS farm, verify that you can establish TLS connections from the server hosting the PCoIP Connection Manager to the PCoIP agent listening on ports 4172 and 60443:
openssl s_client -connect <host-ip-address>:4172
openssl s_client -connect <host-ip-address>:60443
Verifying Connection Broker Availability¶
If you are using a connection broker and the firewall is configured correctly, then verify you can establish a TLS connection from the server hosting the PCoIP Connection Manager to the connection broker listening on port 443:
openssl s_client -connect <broker-ip-address>:443
Verifying PCoIP Connection Manager and Security Gateway Status¶
To verify the PCoIP Connection Manager and/or the PCoIP Security Gateway is running, SSH into the host machine.
-
List the running services in Docker: to verify that the
pcoipcm_cmand/orpcoipcm_sgservices are running:docker service lsYou should see the
pcoipcm_cmand/orpcoipcm_sgservice in the response, similar to the following example:ID NAME MODE REPLICAS IMAGE PORTS 34iefjidf pcoipcm_cm replicated 1/1 cloudaccessmanager.azurecr.io/pcoip-cm:5-release 54ibvbbdt pcoipcm_sg replicated 1/1 cloudaccessmanager.azurecr.io/sg:3-release
Verifying PCoIP Connection Manager Web Application Status:¶
-
Establish a TLS connection using the openssl
s_clientcommand:openssl s_client -connect 127.0.0.1:443 -
When the SSL connection is established, copy and paste the following text to issue a dummy HTTP POST command:
POST /pcoip-broker/xml HTTP/1.1 Host: localhost Content-type: text/xml; charset=UTF-8 Content-Length: 39 <?xml version="1.0" encoding="UTF-8"?>- If the PCoIP Connection Manager is operational, you will receive an XML response containing an
<error-resp>element. -
If the PCoIP Connection Manager is not operational, check the logs of the PCoIP Connection Manager and PCoIP Security Gateway containers:
docker logs <CONTAINER_ID>
- If the PCoIP Connection Manager is operational, you will receive an XML response containing an
PCoIP Client cannot launch a session to the Agent with Horizon Broker¶
In this scenario, ensure that the Horizon Agent and the PCoIP Agent are on the same machine. There are some cases where in you could come across some errors. Some of those situations are as follows:
Windows Logs for PcoIP Agent and Horizon Broker can be found in c:\ProgramData\VMware\VDM\logs.
Case 1:
- Navigate to Servers and click Connection servers.
- Select the Connection Server and check the Use secure tunnel connection to machine checkbox and click Use Blast Secure Gateway for all Blast connections to machine.
This results in a following error:
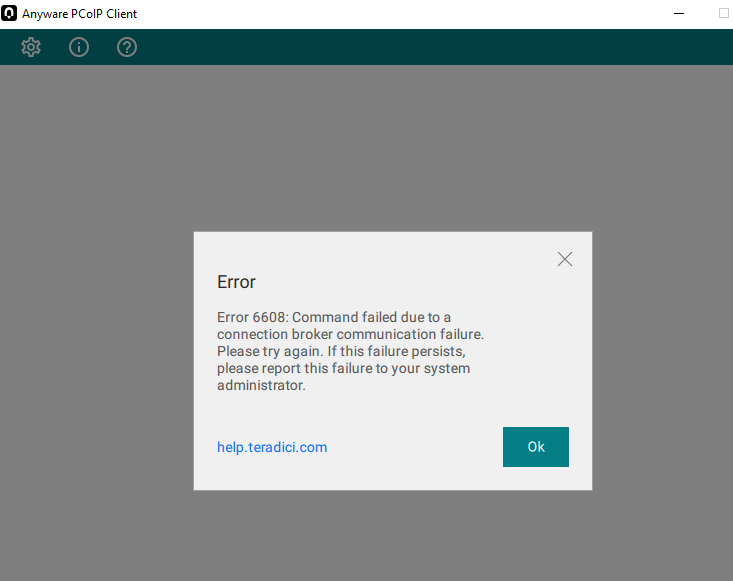
Logs:
2023-05-09T16:01:42.745Z 89c2df80-d0b0-103b-8473-000000000000 s=0002 c=0011 ERROR [app=MCM]baseclient.ClientRequest.<anonymous>: socket hang up
2023-05-09T16:01:44.747Z 89c2df80-d0b0-103b-8473-000000000000 s=0002 c=0011 WARN [app=MCM]baseclient.Timeout._onTimeout: Retry attempt #1 of 3. Reason: timeout
2023-05-09T16:02:44.756Z 89c2df80-d0b0-103b-8473-000000000000 s=0002 c=0011 ERROR [app=MCM]baseclient.ClientRequest.<anonymous>: socket hang up
ERROR [app=MCM]baseclient.retry: Failed to communicate with Broker [https://10.128.24.7:443] because of timeout.
<err-detail>Timeout to communicate with Broker</err-detail> </error-resp> </pcoip-client>
2023-05-09T16:04:56.788Z 89c2df80-d0b0-103b-8473-000000000000 s=0002 c=0011 ERROR [app=MCM]baseclient.ClientRequest.<anonymous>: socket hang up
Case 2:
- Navigate to Servers and click Connection servers.
- Select the Connection Server and check the Use secure tunnel connection to machine checkbox and click Use Blast Secure Gateway for only HTML Access connections to machine.
This results in a following error:
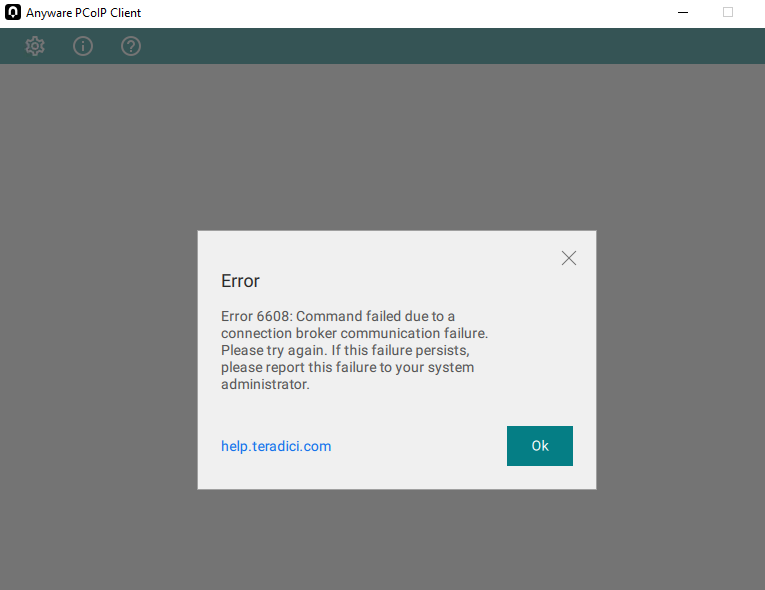
Logs:
2023-05-09T16:12:48.450Z 13bf7800-d0b2-103b-9dc1-000000000000 s=0003 c=0016 ERROR [app=MCM]baseclient.ClientRequest.<anonymous>: socket hang up
2023-05-09T16:12:50.450Z 13bf7800-d0b2-103b-9dc1-000000000000 s=0003 c=0016 WARN [app=MCM]baseclient.Timeout._onTimeout: Retry attempt #1 of 3. Reason: timeout
2023-05-09T16:16:02.475Z 13bf7800-d0b2-103b-9dc1-000000000000 s=0003 c=0016 INFO [app=MCM]brokerprotocol.pbpErrorHandler: Sending response to client (error-resp): <?xml version="1.0" encoding="UTF-8"?> <pcoip-client version="2.1"> <error-resp> <result> <result-id> <err-detail>Timeout to communicate with Broker</err-detail> </error-resp> </pcoip-client>
2023-05-09T16:16:02.478Z 13bf7800-d0b2-103b-9dc1-000000000000 s=0003 c=0016 ERROR [app=MCM]baseclient.ClientRequest.<anonymous>: socket hang up
Other Setting 1:
- Navigate to Settings and Click Global Settings.
- Select Send Domain List and uncheck Hide domain list in client user interface.
This results in a following error:
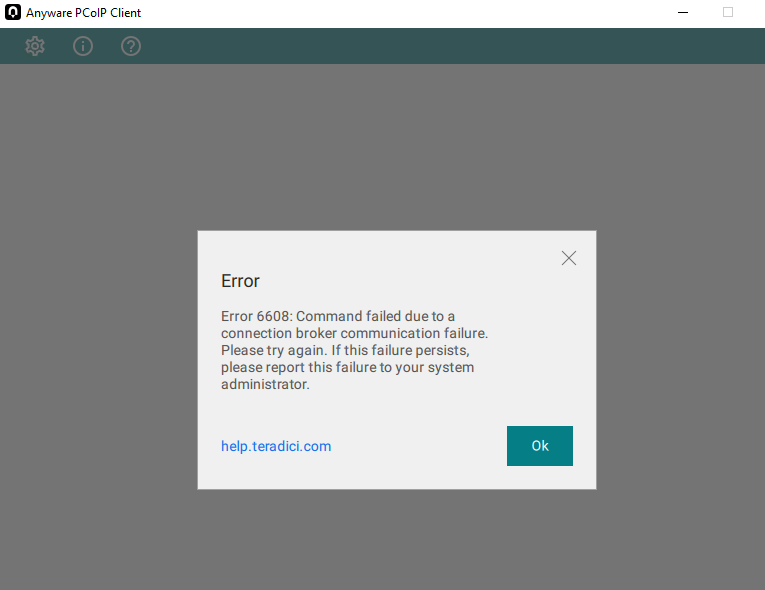
Logs:
<screen> <name>windows-password</name> <params> <param> <name>domain</name> <values> <value>*DefaultDomain*</value> </values> </param> </pa
rams> </screen> </authentication> </configuration> </broker>
//Here in the above log , while authentication it's not the correct domain, it's sending a default domain which led to Authentication failure
//broker doesn't send us the correct domain name
………………………………………….
2023-05-09T16:22:52.292Z 9e54a700-d0b3-103b-b725-000000000000 s=0005 c=0026 INFO [app=MCM]horizonauthenticateresponse.HorizonAuthenticateResponse.handleErrorResponse: Horizon authentication failed with error code AUTHENTICATION_FAILED, e
rror message Authentication failure and user message Authentication can not proceed (Domain name is invalid).
2023-05-09T16:22:52.293Z 9e54a700-d0b3-103b-b725-000000000000 s=0005 c=0026 INFO [app=MCM]requestprocessor.processRequest: Sending response to client (authenticate-resp): <?xml version="1.0" encoding="UTF-8"?> <pcoip-client version="2.1"
> <authenticate-resp method="password"> <result> <result-id>AUTH_FAILED_UNKNOWN_USERNAME_OR_PASSWORD</result-id> <result-str>Authentication failure. Authentication can not proceed (Domain name is invalid).</result-str>
</result> </authenticate-resp> </pcoip-client>
Other Setting 2:
- Navigate to Settings and Click Global Settings.
- Select Send Domain List and check Hide domain list in client user interface.
This settings run successfully.