Configuring firewalld for RPM Installs of Management Console 20.04 or newer¶
As of RPM release 20.04, the Management Console installer does not change any firewall settings, but instead leaves firewall settings to be completed by the administrator. In earlier versions of Management Console, the RPM installer would enable iptables, create and apply a new set of rules that would allow the Management Console to communicate properly.
If you you are using a firewall with Management Console on your Linux PC, you must follow the recommended instructions that show how to create the rules required for Management Console communications. You must add additional rules required to meet the requirements of your corporate security policy. The steps below are for configuring firewalld.
Firewalld default behaviours when enabled
-
All inbound connections are tested against configured rules that have been applied
-
All outbound connections are allowed
-
Rules to allow traffic are added to the default zone. All other traffic will be blocked.
Uninstalling RPM
Uninstalling the Management Console RPM does not completely remove the firewall rules.
To configure firewalld for use with Management Console 20.04 or newer perform the following steps:¶
-
Login to the host computer.
-
Enable firewalld.
sudo systemctl enable firewalld --now-
Get the default zone. If the default zone is trusted it will allow all packets. It is recommended that the default zone is set to public.
sudo firewall-cmd --get-defaultIf default zone is not public, execute the following commands to set the default zone to public.
sudo firewall-cmd --permanent --zone=trusted --remove-service=pcoip-agentsudo firewall-cmd --set-default=publicsudo firewall-cmd --reload
-
-
Get the default zone and assign it to a variable.
def_zone=$(firewall-cmd --get-default) -
Set the log (all denied packets logged together).
sudo firewall-cmd --set-log-denied=all -
Add an interface.
sudo firewall-cmd --zone=$(echo $def_zone) --change-interface=$(ip addr show | grep "state UP" | head -1 | awk -F': ' '{print $2}') -
Enable required ports.
sudo firewall-cmd --zone=$(echo $def_zone) --permanent --add-port={80,443,22,5172}/tcp -
Allow pings.
sudo firewall-cmd --zone=$(echo $def_zone) --permanent --remove-icmp-block={echo-reply,echo-request} 2>/dev/null -
Redirect port 443 to 8443.
sudo firewall-cmd --zone=$(echo $def_zone) --permanent --add-forward-port=port=443:proto=tcp:toport=8443 -
Enable IP Masquerading.
sudo firewall-cmd --zone=$(echo $def_zone) --permanent --add-masquerade -
Redirect Port 80 to 8080.
sudo firewall-cmd --zone=$(echo $def_zone) --permanent --add-forward-port=port=80:proto=tcp:toport=8080 -
Drop incoming packets to 127/8 from other interfaces other than loopback interface.
sudo firewall-cmd --permanent --new-zone loopback 2>/dev/null sudo firewall-cmd --permanent --zone=loopback --change-interface=lo 2>/dev/null sudo firewall-cmd --zone=loopback --permanent --set-target=ACCEPT sudo firewall-cmd --zone=loopback --permanent --add-source=127.0.0.0/8
-
Reload the firewall.
sudo firewall-cmd --reload -
Confirm the rules are applied.
-
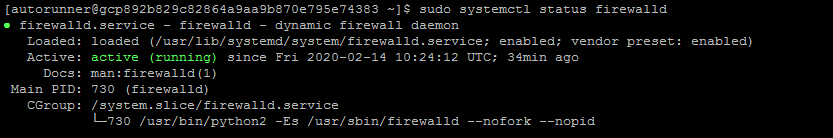
Check the firewalld status is active.
sudo systemctl status firewalld
-
Verify all rules are added in firewalld or not, all rules should be applied.
sudo firewall-cmd --list-all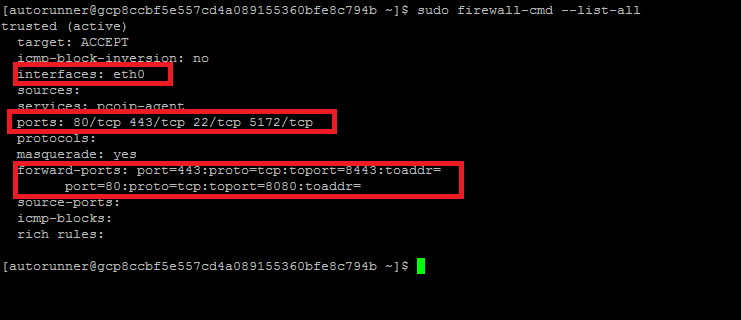
-
-
Install Management Console RPM
sudo MC_NO_CHECK=1 yum -y install curl <RPMLink/RPM local path>
Firewalld Script¶
Teradici has provided instructions to create a script that stops the iptables service, and enables firewalld with the required rules for Management Console to work correctly.
The script file is created and executed using the following steps:
-
Copy the script content and save into firewalld.sh
sudo vi firewalld.sh1. Provide permissions for the script to execute.val1=1 if [ $val1 -eq 1 ]; then systemctl stop iptables || service iptables stop systemctl enable firewalld --now def_zone=$(firewall-cmd --get-default) if [ $def_zone != "public" ] ; then firewall-cmd --permanent --zone=trusted --remove-service=pcoip-agent firewall-cmd --set-default=public firewall-cmd --reload def_zone=$(firewall-cmd --get-default) fi firewall-cmd --set-log-denied=all firewall-cmd --permanent --zone=$(echo $def_zone) --change-interface=`ip addr show | grep "state UP" | head -1 | awk -F': ' '{print $2}'` firewall-cmd --zone=$(echo $def_zone) --permanent --add-port={22,443,80,5172}/tcp firewall-cmd --zone=$(echo $def_zone) --permanent --remove-icmp-block={echo-reply,echo-request} firewall-cmd --zone=$(echo $def_zone) --permanent --add-forward-port=port=443:proto=tcp:toport=8443 firewall-cmd --zone=$(echo $def_zone) --permanent --add-forward-port=port=80:proto=tcp:toport=8080 firewall-cmd --permanent --new-zone loopback firewall-cmd --permanent --zone=loopback --change-interface=lo firewall-cmd --zone=loopback --permanent --set-target=ACCEPT firewall-cmd --zone=loopback --permanent --add-source=127.0.0.0/8 firewall-cmd --reload fi 2> /dev/nullsudo chmod +x ./firewalld.sh -
Run firewalld.sh:
sudo ./firewalld.sh